Additional information has been provided by our panelists to help explain Homomorphic Encryption:
Homomorphic Encryption - Dr. Massimo Bertaccini
Homomorphic Encryption - Dr. Paul Bunn
Encryption and the development of cryptography have been a cornerstone of IT security for decades and remain critical for data protection against evolving threats.
Cryptology long predates today’s encryption algorithms for data stored in our pockets and moving across the web. From Julius Caesar to the Enigma code, cryptographic methods continue to become more complex to the benefit and detriment of various actors.
As cryptanalysts and threat actors poke holes in the latest implementations, it’s natural for the industry and users to upgrade to the most robust available algorithms. Outdated and inadequate cryptographic standards leave organizations and users vulnerable, giving those persistent or capable enough the ability to extract, sell, or ransom sensitive data.
The increasing usage of cloud services and collaboration between companies to monetize data is raising concerns over data privacy. Regulations such as the General Data Protection Regulations (GDPR) aim to protect the privacy of consumers, and businesses pay serious fines in cases of non-compliance. This creates a tradeoff between data privacy and utility for companies.
Homomorphic encryption is an emerging technology that can help businesses to ensure the privacy of their customers without undermining their ability to gain insights from their data.
Join our expert panel in a HOT TOPIC discussion on “The Future of Homomorphic Encryption"
- What is homomorphic encryption?
- How does it work?
- What are the different types of homomorphic encryption?
- Why is homomorphic encryption important now?
- What are the benefits of homomorphic encryption?
- What are the challenges to homomorphic encryption?
- What are alternatives to homomorphic encryption?
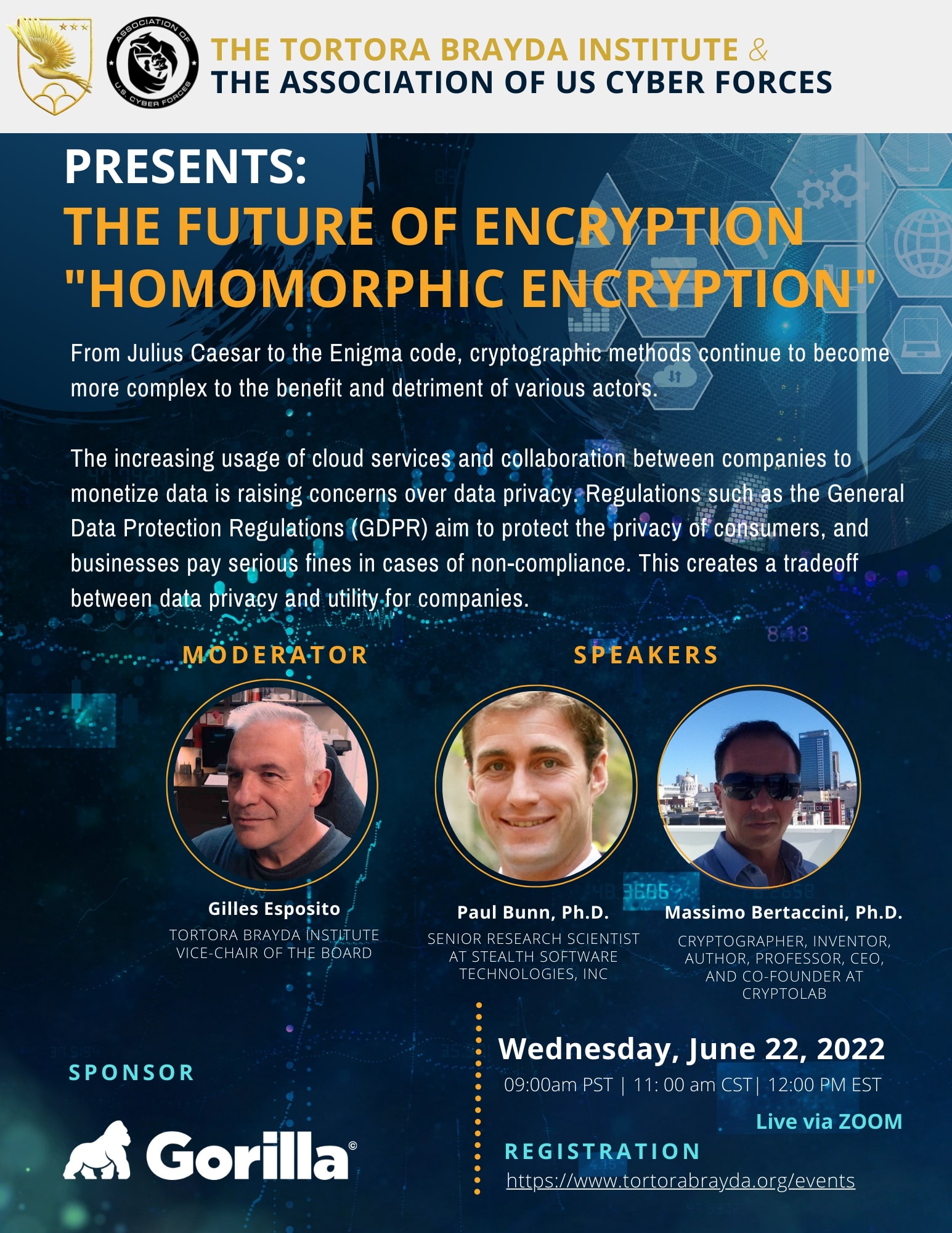
MODERATOR:
Gilles Esposito
Vice-Chair of the Tortora Brayda Institute Board of Directors
Mr. Esposito is a seasoned Technology Industry Professional with Direct and indirect channels sales expert with over 20 years of experience in domestic & international sales, partnerships & alliances management, and business development. He is also a founding member of the NAIC-ISAO and seats on the Board of Directors of The Tortora Brayda Institute
SPEAKERS:
- Massimo Bertaccini, Ph.D.
Cryptographer, Inventor, Author, Professor, CEO, and Co-Founder at Cryptolab
LinkedIn - Dr. Massimo Bertaccini
Massimo Bertaccini, Ph.D. in Financial Computation. Author of a dozen of Patents in Cryptography, A.I., Cybersecurity, and Blockchain. Specialized in Mathematics and Science. Winner of several Prizes, Awards, and Honors, among which "The Silicon Valley Inventors" UST- PO 2016, "The Seal of Excellence" 2016/ 2017 for Horizon 2020.
- Paul Bunn, Ph.D.
Senior Research Scientist at Stealth Software Technologies, Inc
Dr. Paul Bunn obtained his Ph.D. in Mathematics from UCLA in 2010, where his research focused on cryptography and in particular communication across unreliable networks. He worked at Google as a senior software engineer on the Personal Search team, followed by two years as an Applications Specialist in the Department of Biostatistics at UNC-Chapel Hill. Dr. Bunn has spent the past six years in his role as Senior Research Scientist at Stealth Software Technologies, Inc., serving as PI on several government contracts related to cybersecurity and computing on encrypted data.
HISTORY
In 1978, Rivest and Adelman published additional research on a cryptographic method dubbed homomorphic encryption. However, it wasn’t until 2009 that a graduate student published research on fully homomorphic encryption (FHE) and set off an exploration period.
Unlike conventional cryptography, homomorphic encryption allows for a set of limited operations on ciphertext without decrypting the message. Homomorphic models include partial homomorphic (PHE) for a single operation, somewhat homomorphic (SHE) for two functions and FHE for the broadest operational control over encrypted data.
More than a decade later, companies like Google, IBM, and Microsoft continue to explore FHE capabilities where an organization can process specific data within an encrypted message while maintaining the integrity of the data. FHE remains a maturing cryptographic system with little evidence to date of widespread adoption.